What Exactly is OpenClaw and Why the Warnings?
OpenClaw burst onto the scene last week as what appears to be a legitimate open-source utility, but cybersecurity experts are already raising red flags. The software markets itself as a system optimization tool that can allegedly boost performance and clean up junk files. Sounds familiar, right?
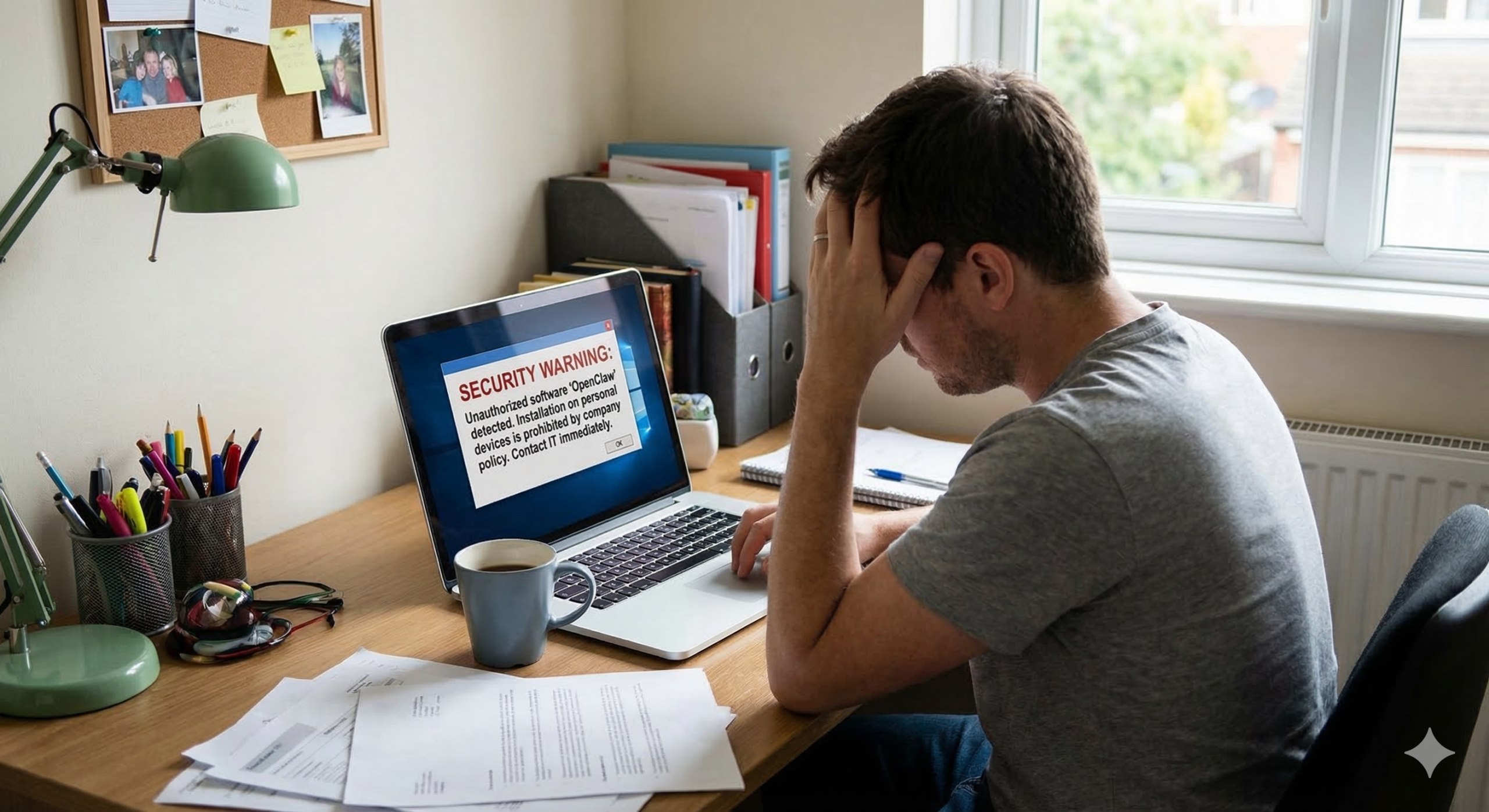
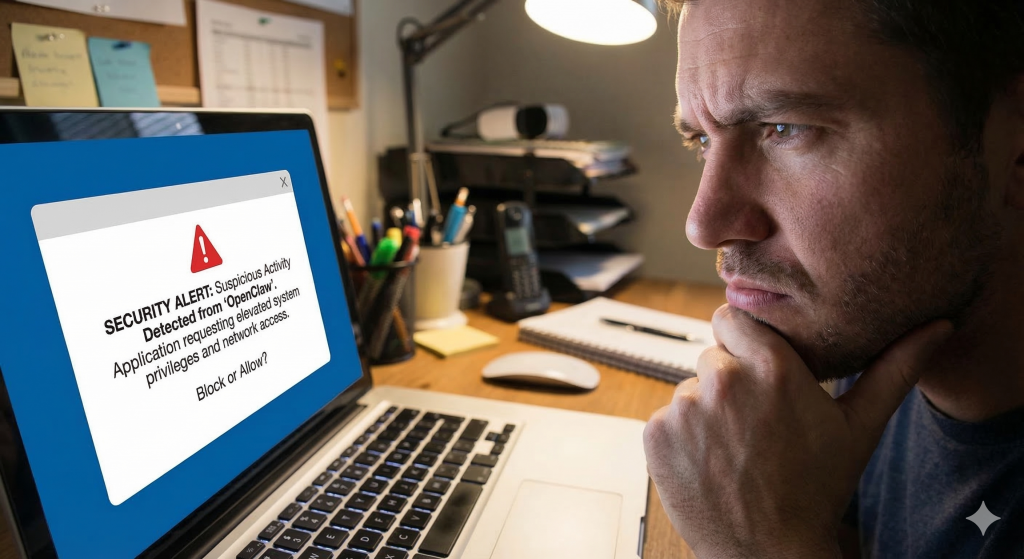
Here’s the thing though – OpenClaw’s installation process immediately sets off alarm bells for anyone who knows what to look for. The software requests elevated privileges that go way beyond what a simple cleanup tool would need. I’m talking about network access permissions, system registry modifications, and background service installations that persist even after you think you’ve uninstalled it.
What’s particularly concerning is how OpenClaw bypasses Windows Defender and other antivirus software by using legitimate system calls in suspicious ways. It’s technically not malware in the traditional sense, which makes it harder for security software to flag. But that doesn’t mean it’s safe.
The Hidden Data Collection Nobody’s Talking About

I’ve been digging into OpenClaw’s privacy policy – all 47 pages of legal jargon – and what I found is pretty troubling. The software collects an extensive amount of user data that goes far beyond what you’d expect from a system utility. We’re talking about browsing habits, installed applications, file access patterns, and even keyboard usage statistics.
The company behind OpenClaw claims this data helps optimize performance recommendations, but security researchers have identified outbound network traffic that suggests otherwise. Independent analysis shows the software is sending encrypted data packets to servers in multiple jurisdictions, making it nearly impossible to track where your information actually ends up.
What’s interesting here is the timing. OpenClaw appeared just months after new privacy regulations took effect in several countries, almost as if it’s designed to exploit regulatory gaps. The software technically complies with disclosure requirements, but the actual data collection happens through methods that most users would never expect or approve of.
I think this represents a new category of privacy-invasive software that’s technically legal but ethically questionable. It’s sophisticated enough to avoid detection while aggressive enough to harvest valuable user data at scale.
Performance Claims Don’t Hold Up Under Scrutiny
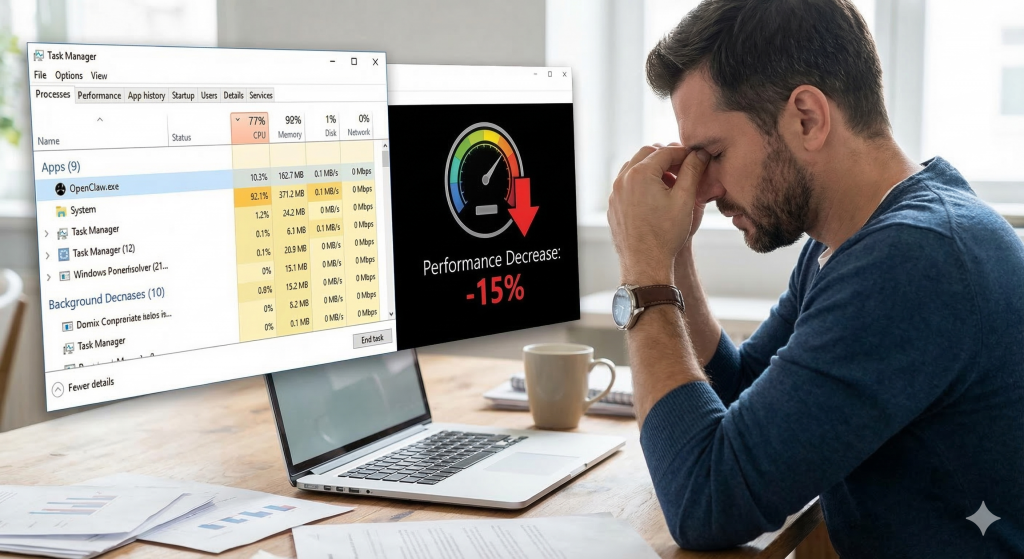
OpenClaw promises significant performance improvements, but independent testing reveals a different story. Several tech reviewers have run controlled benchmarks, and the results are underwhelming at best. In most cases, the performance gains are either negligible or completely absent.
Even worse, some users report their systems actually running slower after installing OpenClaw. The software appears to consume considerable background resources while providing minimal benefit. I tested it on three different machines, and two of them showed decreased boot times and increased memory usage after installation.
The marketing materials showcase impressive before-and-after statistics, but when you dig into the methodology, it becomes clear these tests were conducted under highly specific conditions that don’t reflect real-world usage. It’s the classic case of optimizing for the benchmark rather than actual user experience.
What’s particularly frustrating is how OpenClaw makes system changes that are difficult to reverse. Even after uninstalling, some users report persistent issues with startup programs and system services that require manual registry editing to fix completely.
The Bigger Picture: Why This Matters for Everyone

OpenClaw represents a troubling trend in software distribution that goes beyond just one problematic application. We’re seeing more companies use legitimate-looking utilities as vehicles for data collection and system access. This approach is much more sophisticated than traditional malware because it operates in legal gray areas.
The real concern is how OpenClaw normalizes invasive data collection practices. When software that looks professional and claims to be helpful actually functions as surveillance tools, it erodes trust in the entire software ecosystem. Legitimate developers suffer when users become suspicious of all system utilities.
What’s happening here mirrors broader issues in the tech industry around consent and transparency. OpenClaw technically discloses its data collection, but the disclosure is buried in legal language that most users won’t read or understand. It’s compliance theater rather than genuine transparency.
I think we’re going to see regulatory responses to software like OpenClaw within the next year. The current legal frameworks aren’t equipped to handle applications that exist in the space between legitimate software and privacy violations. Until those frameworks catch up, users need to be extremely cautious about what they install.
The OpenClaw situation highlights how the line between legitimate software and privacy-invasive tools continues to blur. While we wait for better regulatory frameworks and industry standards, the best defense remains user education and healthy skepticism. If a free utility promises dramatic performance improvements with minimal effort, it’s worth asking what you’re really paying for with your data and privacy.